The latest in AWS, CodeBuild

As an enthusiast of cloud and cloud-related technologies, I keep track of conferences and symposiums in this domain. AWS re: Invent is the most significant event in this regard by Amazon (Amazon Web Services) The main event was held in Las Vegas from Nov 29 to Dec 2, 2016. The event is also educational as it showcases the latest updates and trends in AWS with keynote announcements. I was unable to be a part of the event, but I followed the updates happening over Twitter, FB, Youtube, and various other blogs. Of the many new updates that were presented this year, CodeBuild Service caught my attention. In simple terms, the service automatically compiles lines of code written by the developers and runs test cases on it. The service has the ability to run on lesser popular languages through a docker image. CodeBuild works seamlessly with CodeCommit, CodePipeline, and CodeDeploy i.e. other AWS tools for storing, building, and deploying code. The combined set of the above assists the developer in every stage of code development, deployment, and code updates. In tune with the principle of cloud computing, the service is scalable and has the ability for automatic resource termination and instantiation, contrary to the “set and forget” model. The service is charged by the minute. Codebuild currently works on Linux. Looking forward to Windows support in the future. Jordan Novet and Jeff Barr, your articles have been a big inspiration for me to have an up-close look at CodeBuild. I plan to work/experiment with the tool and shall post updates in the upcoming articles.
7 Cloud Computing Security Concerns

Cloud computing security is probably the most important area of concern for most businesses that are evaluating a cloud computing strategy for themselves. “The Cloud” essentially provides the option of storing and processing data on a device that is externally located and may or may not be shared. The extent to which the processing & storage is being shared determines the cloud deployment model: Public, Private & Hybrid. However, in the purest sense cloud is a shared & external location for the storage and processing of data. Now because the data is externally located and also shared, naturally means that the risk profile of the data has increased. But the increase in risk profile doesn’t mean that cloud computing is unsecure. In fact, given that most cloud computing service providers recognize the security risks of the cloud, they try to put in place time and effort to make their service offerings completely secure. Because of this concerted effort in this direction, it may actually be the case that your data may be more secure on a cloud server rather than on your office premise. So it goes without saying that all service providers are making effort in making their cloud secure. But it also remains a fact that cloud computing increases the risk profile of your data and as such all businesses should recognize these concerns and try and evaluate their cloud provider on their ability to address these concerns. With this blog, we attempt to explain “Gartner’s 7 cloud computing security concerns” and also prompt the questions that should be posted to cloud service providers in order to evaluate their security: Gartner’s 7 cloud computing security concerns 1. Privileged user access The cloud takes your data physically away from you. You are no longer the custodian of your data. The custody of your data now is with the administrator appointed by your cloud service provider. It is this person or set of individuals who needs to be scrutinized before you trust your data with them. It is therefore essential to ask your cloud service provider for information on the people who will administer the cloud. There should be a mechanism by which these individuals are screened, evaluated, and appointed. Any service provider who is not upfront about its recruitment process and employee profile cannot be trusted with your data. 2. Regulatory compliance There are external auditors who scrutinize the cloud computing security measures of any cloud service provider. They are an independent source of information on the cloud’s security. Any service provider you are considering should be willing to go through such audits. In cases the audit has already been done, you should request for the audit report to be shared by the cloud service provider. In fact, cloud service providers should willingly participate in audits. The audit can showcase and certify the cloud’s security. 3. Data location Location is important from the legal jurisdiction standpoint. With the cloud, the data can be physically located anywhere. It depends on where the service provider is having its data center. Let’s suppose the data center is located in a place where the legal system is lax. In such a situation the cloud service provider can escape prosecution, in case it is complicit in knowingly or unknowingly compromising the security of your data. To avoid such a situation you should request your service provider to keep your data in a location that you are comfortable with and also execute proper agreements with your service provider which will force it to abide by the rules & regulations in the location. 4. Data segregation The cloud in its purest form (public cloud) is shared between organizations. There are ways in which the data can be segregated from each other. It is important to know the ways the service provider is ensuring the data is segregated. Encryption is one such way. However incorrect encryption can almost make the whole data set unusable. 5. Recovery Generally, cloud service providers replicate the data on at least a couple of locations. This is a way to ensure that the data can be recovered from a separate location due to any accidental loss. Any service provider who doesn’t back up the data is an immediate red flag. You should, therefore, request your service providers for information on the places where your data is getting backed up. If in case your data is not getting backed up, you should discontinue working with that service provider immediately. 6. Investigative support There are various ways in which data security can be insured on the cloud. You can do deterrent control by warning users of the consequences of stealing your data. The largest subset of deterrents is preventive control, like with the point we discussed on screening administrators. Then there is detective control by using techniques to monitor intrusion attempts. Finally is the question of corrective control, for which you need investigative support. Once you have suffered any data breach, investigative support enables you to find out the problem and limit its loss or prevent it from happening again. Your cloud service provider should ideally be under contractual obligation to co-operate in any investigation as and when required by you. 7. Long-term viability You should also spend the time to investigate the market and financial standing of your service provider. It should not be such that the provider is a newbie in the market with nothing to lose. If such a provider sees a sustained cycle of financial distress it is likely to fold and leave you high & dry. Also, the service provider should have deep pockets to withstand a sustained period of stress. Need help with Cloud? Reach us at mktg@inapp.com or Contact us
Managed Vs Unmanaged Cloud – An Infographic
There are lots of numbers involved when migrating to the cloud. There needs to be an important choice to be taken between a managed cloud (where the vendor manages, patches, and troubleshoots your cloud surrounding) or an unmanaged cloud (where your IT department has to do that on its own). Here’s an infographic focusing on the key differences. Managed Vs Unmanaged Cloud Analyzing the total cost of ownership when migrating to the cloud. The Extra Edge A managed cloud enables businesses to spend time on strategic work instead of baseline operations like procuring and maintenance. Saving Time over Cost Deploy hardware faster Best-in-class functionality Virtualization and Automation Brings down costs in procuring, testing, and deploying Adaptability With the flexibility for internal IT staff to focus on more value-add products, the managed cloud allows businesses to quickly react to market shifts while preparing for future demands. Employee Comfort Developing new competencies is an important step in increasing employee satisfaction, as it allows employees to gain new skill sets. Need help? Contact us now!
SaaS Testing Using Cloud: An Emerging Discipline
Introduction More than a decade ago, in the era when technology evolved to bring in virtualization in the mode of cloud computing, a funny reply came from the owner of an organization when one of his subordinates shared a thought on migrating their services to the cloud. The reply was, “I just don’t trust keeping our data in the cloud. Plus if we got rid of the server, where would we keep the coffee maker!!! ?”. Later, after a decade, we witnessed that the cloud and its services became a game-changer and the deciding factor in the existence of many software organizations. Organizations can meet business demands in a quicker way and by achieving scalable costs by using Software as a Service, thus helping them to focus on their core business. Software as a Service (SaaS) testing using the cloud minimizes the hiccups that arise in traditional testing thereby providing infinite effective storage and flexibility via distributed environment. What is SaaS Testing? SaaS is a software distribution model in which applications are hosted by a vendor or service provider and made available to the customers over a network, typically the Internet. SaaS Testing refers to the methods used to ensure that applications built using the software as a service model of development function as designed. It also ensures the performance, security, and reliability of an application by leveraging the cloud-based infrastructure and computing resources to perform for a regular on-premise platform. Objectives of SaaS Testing should be: SaaS deployments should take less time than on-premise software deployments. Software hosted on the cloud should be highly secure, scalable, and reliable. The extent to which the SaaS solution can be customized Why SaaS Testing? SaaS testing is intended to be a speedy and productive manner to get applications released to customers. In agile methodology testing and quality assurance (QA) has become more critical as applications are delivered more rapidly. Since the number of testing increases, more focus should be provided on the quality of the applications developed in a quick and efficient manner. A. Efficient Load Testing There will be times when we are unable to predict the number of users who use the application. So in order to perform efficient load testing, we can approach any cloud service where we can simulate users and easily scale up to the desired load to measure the performance of the application under a large number of concurrent users. B. Replicate real-world usage It also helps users’ data to be moved to large data centers, which are remotely located, with the user being able to access the same anytime needed. C. Reduces the direct price of the equipment It reduces the direct price of equipment maintenance and management and helps attain rapid ROI on application assets and brings about faster time to market. Types of SaaS Testing Functional Testing SaaS Functional testing is performed for both remote and local applications. It consists of testing all features of the system including hardware and software testing. The different types of functional testing are System, Integration, and User Acceptance Testing. Non-functional Testing This type of testing is done to ensure that a web application meets the specified requirements; the way an application operates, rather than the specific behaviors of that application. It includes Security testing, Stress testing, Load Testing, and Performance Testing. Ability Testing Techniques Ability Testing Techniques ensure that the user receives appropriate services from the cloud environment on demand. Under this category, Compatibility and Interoperability Testing, Disaster Recovery Testing, and Multi-Tenancy testing are performed. Testing as a Service in Clouds TaaS aka Testing as a Service is a subset of a SaaS offering, allowing groups to outsource their entire test effort. With this model, the manpower and expertise required to execute the test are provided. This type of cloud testing is an approach that can also be used for specialized types of tests, such as performance, mobility, or security testing. The execution can be performed either on the client site or remotely from the outsourced provider’s test lab/facilities. TaaS Architecture Points to successful SaaS testing Build your understanding of the cloud Before moving your project to the cloud the objective and the strategy should be clearly defined. The organization or the management team should do formal research about the business needs and the limitation of moving the project to the cloud. Formulate your testing strategy The type of test and the risk involved during the test should be analyzed by creating a good test strategy. The duration of the usage of any cloud tool should be predefined and well-documented. Select a service provider A service provider has an enormous amount of experience and stability is the prime factor when choosing the vendor. License, cost, set-up, and tear down of the environment should be thoroughly scrutinized. Execute the test Companies should plan for optimal utilization of test infrastructure since it is a critical phase where applications are tested according to the defined test strategy. Monitor and analyze test results Test results should be monitored in real-time to understand and react to capacity – or performance-related issues. Cloud Testing Tools Needless to say, the emerging popularity of cloud testing has given rise to a set of cloud-based testing tools in the market. The right choice of testing tools depends on multiple parameters including application architecture, context, and customer needs. Here are some of the highly popular cloud-based software testing tools. 1. SOASTA Cloud Test It enables four types of test automation on a single web platform – Mobile Functional & Performance testing and Web-based Functional & Performance testing. 2. LoadStorm It is a load-testing tool for web and mobile applications. It is easy to use and cost-effective. It is ideal to check performance under excessive traffic or usage. 3. BlazeMeter It is used for end-to-end performance and load testing of mobile apps, websites, and APIs. It is JMeter compatible and can simulate up to 1 million users. 4. Nessus It is a widely used vulnerability scanner that
How to develop Cloud App Using Microservices Architecture

Cloud-based Apps developed using Microservices architecture are a radical change from our present-day Monolithic, on-premise applications. These next-generation applications are providing the software with the robustness and agility it requires in today’s world. These applications are also much cheaper to develop and maintain. Though these applications are economical, they pack a punch! Am I sure you must be mighty intrigued? So let me explain these applications in detail and then we will also discuss how we can develop such a power-packed application. What do we mean by calling today’s applications “Monolith”? A Monolith means a single large unit. Today’s Monolithic applications are as depicted below: The application that you may be having today generally has 3 parts. The first part is the front-end-user interface. It is also referred to as the client part. It is a web interface it will be made up of an HTML page and some JavaScript code running on the client-side machine. The second part is the database, which is a series of related tables. Finally, there is the back end or the server end. The server end is the brains of the operation. It contains all the business logic of the application. A request would first come in from the front end and will be processed by the back end. Whatever information and request come from the front end is first brought to the back end, additional information is then queried from the database, business logic is then executed, the processed information is updated to the database, and request information is displayed back at the front end. Hence the back end becomes like a huge single machine, with one single process doing everything. There are numerous problems with such a structure. As stated before one error can crash the whole application. Hence the application is not robust. Errors are difficult to find and responsibility for failure is difficult to assign. Scaling up is a huge problem. It requires huge instances of the entire application to be created each time. Small changes require the entire application to be changed. These problems are extenuated in today’s environment where we expect the application to continuously change according to real-time requirements. The application is deployed in the cloud and is directly accessible to the user instead of being installed on a local computer. Continuous development is ongoing in real-time as per the requirements of the consumer. It means that there are chances of breakages. Continuous development cannot happen if we have breakages that will bring down the entire system. Microservices Architecture The problems stated above have caused a movement toward a Microservices architecture. Microservices are multiple small modular units, designed to do one specific thing. They are completely independent in that they have their own OS, platform, framework, and runtime. All of it is packaged as one single executable unit. It is also independent of the other Microservices. The way these processes communicate is through platform-agnostic API calls. The protocol is generally Restful state transfer (Rest). These calls generally don’t require the processes to create a state. Thus processes don’t lock out. Because the calls are platform agnostic, the developers can independently develop separate processes in the platform they are comfortable with or is more suitable for that particular process. With cloud apps, the infrastructure itself becomes lines of code. This gives the developers immense flexibility. The cloud is also enabling container technology. The containers have both the OS and the line of executable code to run on the OS. Now developers are using the two (containers & cloud) to create code that is on their own platform and language. There are many benefits to this architecture. Scaling out becomes much easier. Instead of creating multiple instances of the whole application, it is now possible to create multiple instances of the particular services that require to be scaled. The overhead of creating additional virtual machines is avoided. New processes can run on the same virtual machine. Fault tolerance increases much fold because each process has been separated. Now the failure of a particular process doesn’t affect the other. Lastly, by adopting microservices, you can invest in reusable building blocks that can be in continuous development. Each microservice becomes like a Lego block that can be plugged into an application stack. By investing in a set of core microservices, you can assemble them to build cloud apps catering to a variety of uses. Also because it is hosted on the cloud and is highly robust, you can keep the app in continuous development. How to develop cloud apps using Microservices? Now one can easily take an app to the cloud without venturing into a microservices architecture. If you do so you can immediately gain the benefits of getting hardware flexibility and cost savings. However, this is the only fraction of the benefit possible with the cloud. It is a very sub-optimal use of cloud computing capability. In such a scenario an approach proposed by folks from Carnegie Mellon University is “the horseshoe.” As the picture above shows, one should begin at the Technical Architecture level to start a cloud app development. Migrate to the cloud your existing app. Then you can proceed to change the application itself making it microservices oriented and thereby making changes at the architecture level. As we move up each level the path becomes longer and costlier. But, this way old legacy system which has become gridlocked for change, due to it containing critical code, for which expertise has gone away due to retiring personnel, can be unlocked and changed to a modern cloud app. Have questions? Contact the cloud computing experts at InApp to learn more.
Chef vs Puppet vs Ansible | A Comparison Infographic
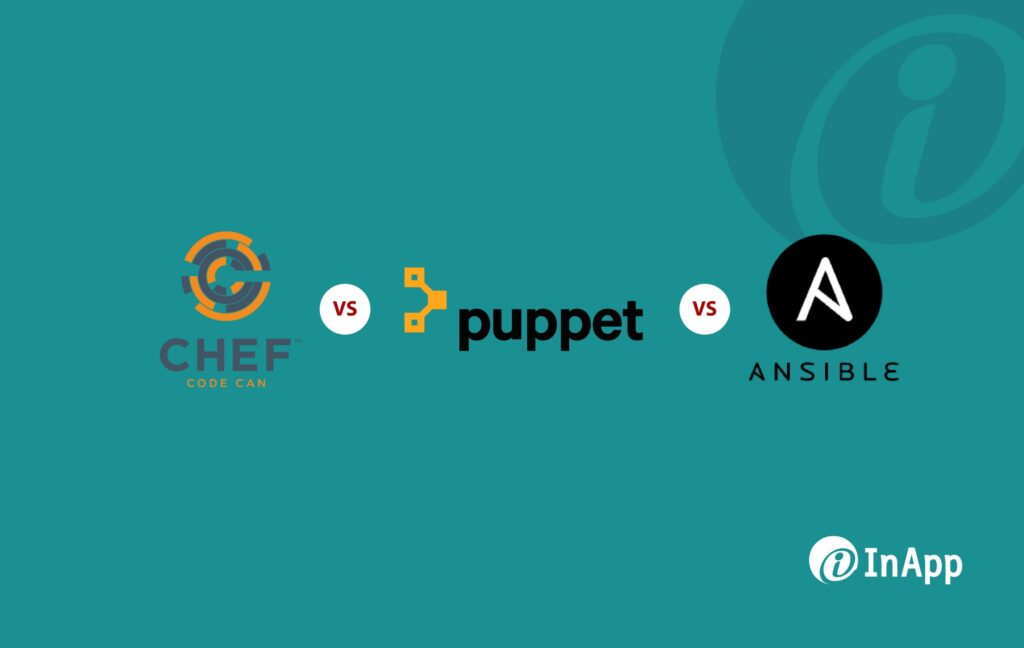
Chef, Puppet, and Ansible all are open-source deployment management tools, used to manage competently large-scale server infrastructure, by enabling speed and ensuring reliability, with very minimal input from developers and system admins, using different paths. Initial Setup Ansible: Less concentration on configuration managementPuppet: Simple installation and initial setupChef: Initial setup is complicated Interface Ansible: Simple and structured (built on Playbooks)Puppet: Very instinctive and complete Web UIChef: Designed exclusively for programmers Security Ansible: High Security with SSHPuppet: VulnerableChef: Chef Vault Scalability Ansible: YesPuppet: YesChef: Yes Code Ansible: Written in PythonPuppet: Built with RubyChef: Configured in Ruby DSL Pricing Ansible: Starts at $5000 per yearPuppet: Standard pricing starts at $120 per nodeChef: Standard pricing starts at $72 per node Feature Ansible: Automated workflow option for continuous deliveryPuppet: Strong compliance automation and reporting toolsChef: Offers hybrid and SaaS solutions for Chef server, analytics, and reporting Have questions? Contact the technology experts at InApp to learn more.
The 4 Key Factors to Keep in Mind while Choosing the Right Cloud Service Provider

The following are the 4 Key Factors you should keep in mind while choosing a Cloud Computing Service Provider. 4 Key Factors when choosing Cloud Computing Service Providers are: Business Health and Process Business knowledge and technical know-how Compliance audit Financial health Organization, governance, planning, and risk management Trust Technical Capabilities Change management Hybrid capability Ease of deployment, management, and upgrade Standard interfaces Event management Security Practice Security infrastructure Security policies Identity management Data backup and retention Administration and Support Performance reporting Service Level Agreements (SLAs) Billing and accounting Resource monitoring and configuration management Have questions? Contact the cloud computing experts at InApp to learn more.
6 Points to Remember Before Deploying Cloud Apps – An Infographic

6 Points to Remember Before Deploying a Cloud App Evaluate the different ways employees, partners, and customers access information and then map out data access and sharing points. Implement during slow periods – If people are focused on completing year-end, mission-critical activities, it wouldn’t be the best time to implement cloud. Don’t roll out all features at once – It’s just too much for the end-user to absorb. Prepare for change management – Cloud Computing providers typically update their applications a few times a year. A cloud app user should have an update process, test scripts, and a team ready to respond. Create a repeatable process for testing and deploying product updates, and don’t rush it. Communicate any resulting shifts in job responsibilities. Have questions? Contact the cloud computing experts at InApp to learn more.
Amazon Web Services – AWS’s Latest Additions
AWS’s Latest Additions Athena Start querying data instantly. Get results in seconds. pay only for the queries your run. Blox Open Source scheduler for Amazon EX2 container service. EC2 F1 Instances Run custom FPGAs in the AWS Cloud. Glue Easily understand your data sources, prepare the data, and load it reliably to data stores. Lambda@Edge Allows you to run Lambda functions at the AWS Edge locations in response to CloudFront events, without provisioning or managing servers, by using the AWS Lambda serverless programming model. Rekognition Deep learning-based image recognition – Search, verify, and organize millions of images. Snowball Edge Petabyte scale data transport with onboard storage and computing. Pinpoint Targeted push notifications for mobile apps. Polly Turn text into lifelike speech using deep learning X-Ray Analyze and debug production, and distributed applications. Have questions? Contact the cloud computing experts at InApp to learn more.
Key Steps for Successful ERP Cloud Migration
Key Steps for Successful ERP Cloud Migration Have questions? Contact the cloud computing experts at InApp to learn more.
