From Resilience to Growth: How Industry 4.0 Can Help the Manufacturing Sector Navigate Recessions
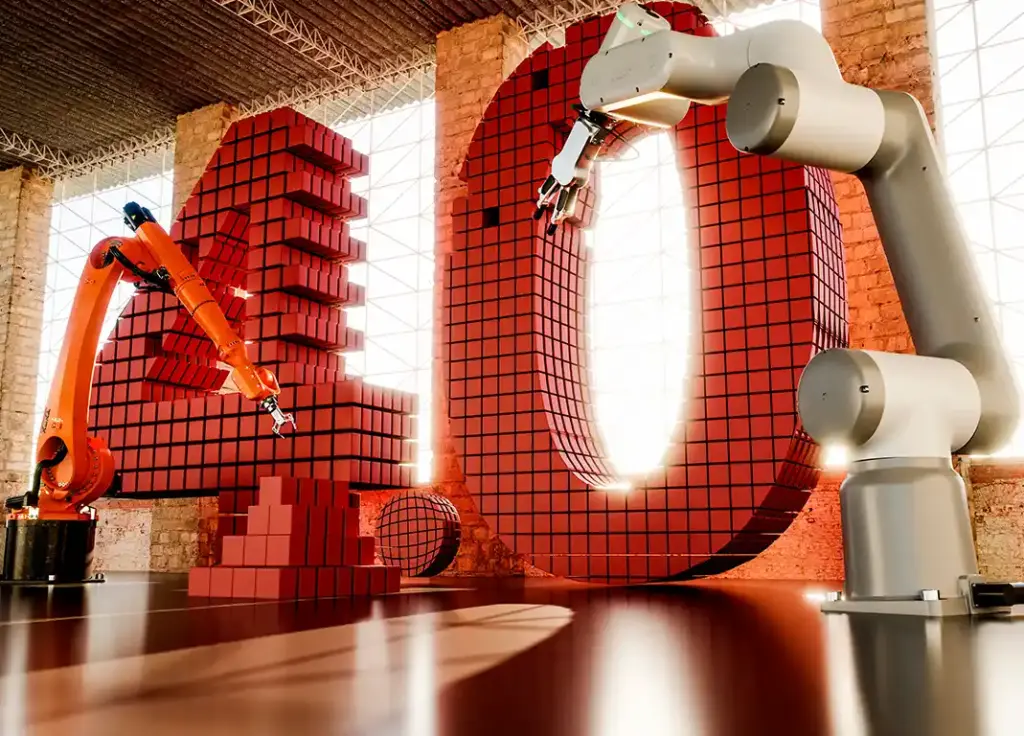
In recent years, Industry 4.0 has emerged as a transformative force in the manufacturing sector. This concept, also known as the fourth industrial revolution, refers to the integration of advanced technologies such as Artificial Intelligence, the Internet of Things (IoT), and Cloud Computing into manufacturing processes. The goal of Industry 4.0 is to create a more interconnected and efficient manufacturing ecosystem, where data can be collected and analyzed in real-time to optimize production and reduce costs. The manufacturing sector is no stranger to economic challenges, and recessions can be particularly tough on manufacturers. During a recession, demand for goods and services typically decreases, leading to reduced revenue and profits for businesses. This shift can result in layoffs, bankruptcies, and a general slowdown in economic activity. However, the manufacturing sector has historically shown resilience during times of economic uncertainty, due in part to its ability to adapt to changing market conditions. In this blog post, we’ll explore how Industry 4.0 can help manufacturers not only weather recessions but also emerge stronger on the other side. By adopting the latest technologies and tools, manufacturers can enhance their resilience and pivot their operations toward growth. We’ll discuss specific examples of how Industry 4.0 is changing the manufacturing landscape and explore the potential benefits for businesses of all sizes. The Resilience of the Manufacturing Sector in Recessions The manufacturing sector has shown remarkable resilience during past economic downturns. For example, during the 2008 financial crisis, manufacturing output initially fell sharply, but it recovered more quickly than other sectors, and by 2010, it had surpassed pre-crisis levels. Manufacturers are often able to adapt their operations to meet changing market conditions, whether that means reducing costs, diversifying their product lines, or exploring new markets. Manufacturing is also a critical part of many supply chains, which means that disruptions can have ripple effects throughout the economy. As a result, policymakers often focus on supporting the manufacturing sector during recessions to promote economic stability. However, not all manufacturers are equally resilient, and some may struggle more than others during a recession. Here’s where Industry 4.0 can help: by adopting the latest technologies and tools, manufacturers can enhance their resilience and position themselves for long-term success. What is Industry 4.0? At the risk of oversimplifying a complex subject, Industry 4.0 is essentially about automating business ecosystems with the help of emerging technologies such as the Industrial IoT (IIoT), big data (and analytics), cloud computing, robotics, digital twins, artificial intelligence, augmented reality, and cybersecurity, to name a few. Industry 4.0, also known as the fourth industrial revolution, refers to the integration of advanced technologies such as artificial intelligence, machine learning, the IoT, robotics, and data analytics into industrial processes to predict, control, and plan business outcomes. Industry 4.0 is characterized by using cyber-physical systems, which are systems that integrate physical processes with digital technologies. This integration enables industries to optimize their operations, reduce costs, increase efficiency, and improve productivity. These systems are designed to collect, analyze, and communicate data in real time, allowing for real-time decision-making and automation of industrial processes. Some of the key technologies that fall under the Industry 4.0 umbrella include: 1. The Internet of Things (IoT): IoT refers to the network of physical devices, vehicles, and other objects that are embedded with sensors, software, and connectivity, allowing them to collect and exchange data. In manufacturing, IoT can be used to monitor machines and equipment in real time, allowing manufacturers to identify and address potential issues before they become major problems. 2. Artificial Intelligence (AI): AI refers to the simulation of human intelligence in machines that are programmed to learn and make decisions based on data. In manufacturing, AI can be used to optimize production processes, predict maintenance needs, and improve product quality. 3. Robotics: Robotics refers to the use of automated machines to perform tasks that humans typically do. In manufacturing, robotics can be used to automate repetitive or dangerous tasks, freeing up human workers to focus on higher-value activities. 4. Cloud Computing: Cloud computing refers to the delivery of computing services over the internet, allowing users to access and store data and applications remotely. In manufacturing, cloud computing can be used to store and analyze large amounts of data, enabling real-time monitoring of production processes and optimization of workflows. 5. Additive Manufacturing: Additive manufacturing, also known as 3D printing, is a process of building three-dimensional objects by adding layer upon layer of material. Additive manufacturing can be used to create complex parts quickly and with less waste than traditional manufacturing methods. By adopting these technologies and integrating them into their operations, manufacturers can create a more efficient, flexible, and resilient production process that can shift quickly to changing market conditions. This adaptability can be particularly valuable during recessions, when demand for certain products may decrease, and manufacturers need to find ways to reduce costs and optimize their workflows. Industry 4.0 in Practice: Examples from the Manufacturing Sector A generational shift by the application of Industry 4.0 has revolutionized industries such as logistics and transportation, healthcare, manufacturing, and automotive to name a few. This paradigm shift has become even starker with the onset of Covid-19 as evidenced by this article from McKinsey, which shows companies that had already scaled their digital technologies before the pandemic clearly handled the crisis better than those who had not initiated the journey. The benefits of Industry 4.0 are not just theoretical. Many manufacturers have already begun to adopt these technologies and are seeing real-world results. Here are a few examples: 1. Predictive Maintenance: By using IoT sensors to monitor machines and equipment in real time, manufacturers can identify potential issues before they become major problems. This data can help prevent unplanned downtime and reduce maintenance costs. For example, Schindler Elevator Corporation has implemented an IoT-based predictive maintenance system for its elevators and escalators, which has reduced downtime by 20% and maintenance costs by 25%. 2. Quality Control: AI can analyze data from sensors and other sources to identify patterns and anomalies that might indicate quality issues. As a result, manufacturers can catch defects earlier in the production process and improve overall product quality. For example, Siemens uses AI-powered
Hybrid vs Cross Platform vs Native Mobile App Development: How to Choose?
Mobile apps have taken the world by storm, allowing users to access services and information on the go with just a few taps on their screens. According to a report published by Allied Market Research, the global mobile app market size is projected to grow at a compound annual growth rate (CAGR) of 18.4% from $106.27 billion in 2018 to $407.31 billion by 2026. This growth is driven by the increasing adoption of smartphones and the internet, as well as the growing demand for mobile apps in various industries, including healthcare, education, finance, and retail. Businesses can leverage this trend by investing in mobile app development, which provides a direct line of communication with customers, personalized content, and valuable data insights. In this blog post, we’ll delve into the three main categories of app development: We’ll explore the differences between these approaches, and their advantages and disadvantages, to help you make an informed decision when it comes to choosing the best development method for your mobile app project. Whether you’re a business owner, entrepreneur, or developer, this post will equip you with the knowledge you need to make the right choice for your app development needs. So let’s dive in and discover the best approach for your next app project. What Are Native Applications? Native applications are developed specifically for a particular platform or operating system using the programming languages, tools, and technologies supported by that platform. These apps are designed to take full advantage of the device’s hardware and software capabilities, providing faster performance, smoother user experience, and better integration with the OS and other apps installed on the device. Native applications are not just restricted to mobile applications. Instead, they can be developed for various platforms, including desktop operating systems like Windows, macOS, or Linux, and mobile operating systems like iOS or Android. These apps can be downloaded from app stores or installed and launched like any other desktop application, providing access to local resources such as file systems, network connections, and peripherals. Native app development requires specialized knowledge of the platform and programming languages being used, which can make it more time-consuming and expensive than other app development methods. However, the resulting apps offer a high degree of reliability and functionality, making them a popular choice for developers and users alike. Examples of Native Applications Here are some examples of native applications for different platforms: What Are the Advantages of Native Applications? Native applications offer several advantages over other types of apps. What Are the Limitations of Native Applications? Native applications, which are built for a specific platform using the platform’s native development tools and languages, offer many advantages such as high performance and excellent user experience. However, limitations include development costs, longer development timelines, and the need for specialized expertise in each platform’s development tools and languages. Overall, while native apps can offer advantages such as high performance and optimal user experience, their limitations in development cost, time to market, maintenance complexity, limited reach, fragmentation, and potential user experience inconsistencies should be considered when choosing this approach for mobile app development. What Are Hybrid Applications? Hybrid applications are mobile applications that combine elements of both native and web applications. These applications are built using web technologies such as HTML, CSS, and JavaScript, but are also packaged in a native container that allows them to access device-specific features such as the camera, contacts, and GPS. Hybrid applications are designed to provide the best of both worlds: the flexibility and ease of development of web applications, along with the performance and functionality of native applications. Hybrid applications are typically developed using cross-platform frameworks such as Apache Cordova, React Native, and Ionic, which allow developers to write a single codebase that can be deployed to multiple platforms such as iOS and Android. Hybrid applications have become increasingly popular in recent years as they allow developers to create applications that work across multiple platforms without the need to write native code for each platform separately. They are also easier to maintain than native applications as changes can be made to the codebase once and deployed across multiple platforms. Examples of Hybrid Applications There are many popular hybrid applications available on both the Apple App Store and Google Play Store. Examples of popular hybrid applications include: Many other well-known apps, such as Walmart, Airbnb, etc., are also hybrid apps. What Are the Advantages of Hybrid Applications? Hybrid applications offer several advantages over native and web applications. Overall, hybrid applications provide a balance between the flexibility of web applications and the functionality of native applications, making them a popular choice for many organizations. What Are the Limitations of Hybrid Applications? Hybrid apps have performance and user experience limitations due to the additional abstraction layer, compatibility issues, and security vulnerabilities, which may require compromise in development complexity and customization. Here are some of the limitations of hybrid applications. Overall, while hybrid apps can offer some advantages such as easier maintenance and lower development costs, their limitations in performance, user experience, customization, compatibility, development complexity, and security should be carefully considered before choosing this approach for mobile app development. What Are Cross-Platform Applications? Cross-platform applications are designed to run on multiple operating systems and devices, using a single codebase. Cross-platform app development frameworks such as React Native, Xamarin, and Flutter allow developers to build apps that can be deployed to both iOS and Android devices, as well as other platforms such as web browsers and desktop operating systems. Cross-platform apps offer advantages such as lower development costs, shorter time to market, and wider audience reach. However, they may have limitations in performance, user experience, and compatibility with device-specific features and functionalities, which should be carefully considered when choosing this approach for mobile app development. Examples of Cross-Platform Applications Examples of popular cross-platform applications include: What Are the Advantages of Cross-Platform Applications? Cross-platform applications offer several advantages. Overall, cross-platform apps offer advantages in terms of cost, time, audience reaches, maintenance, user experience, and community
Top 7 Cloud Computing Security Risks to Watch for and How to Tackle Them

Cloud computing has become an essential part of modern business operations, allowing organizations to store and access data, applications, and services on remote servers. However, as more businesses adopt cloud technology, the risks associated with cloud computing security are also increasing. According to a report by McAfee, the use of cloud services grew by 50% in 2018, and during the same time period, 83% of organizations experienced a cloud security incident. This statistic highlights the need for businesses to understand the top cloud computing security risks and how to tackle them. In this blog post, we’ll explore the top cloud computing security risks and provide some tips on how to tackle them. You’ll learn the risks associated with data breaches, misconfigured cloud resources, insider threats, and more. We’ll also share some statistics on the impact of these security risks on businesses. By the end of this blog post, you should have a better understanding of the potential security risks of cloud computing and some best practices for mitigating them. So, let’s dive in and explore the top cloud computing security risks and how to tackle them. Top 7 Cloud Computing Risks & Ways to Tackle Them 1. Data Breaches Cloud providers store vast amounts of sensitive data, and a data breach can lead to significant financial loss and reputational damage. Data breaches can occur through a variety of methods, such as phishing attacks, malware injection, and exploitation of vulnerabilities in cloud infrastructure. They can also occur due to human error, such as accidental exposure of sensitive data. Tackling Data Breaches To tackle the risk of data breaches, businesses should implement strong access controls, such as multifactor authentication, to ensure that only authorized personnel can access sensitive data. Encryption of data both in transit and at rest can also help prevent unauthorized access. Businesses should also monitor their cloud infrastructure for suspicious activity, such as unusual login attempts or changes in data access patterns. Another key aspect of preventing data breaches is establishing a clear incident response plan. The incident response plan should outline the steps to take in the event of a data breach, such as who to contact, how to contain the breach, and how to communicate with affected parties. Regular testing and updating of the incident response plan can help ensure that it remains effective over time. 2. Misconfigured Cloud Resources Cloud resources are often misconfigured, which may leave them vulnerable to attack. Misconfigurations can occur in many different areas, such as network security groups, access controls, and encryption settings. Causes of misconfigurations include human error, lack of understanding of the cloud environment, and miscommunication between different teams responsible for cloud infrastructure. For example, consider an improperly configured network security group (NSG) in Microsoft Azure. An NSG is a virtual firewall that can be used to filter network traffic in and out of Azure virtual machines. If an NSG is misconfigured, it can allow unauthorized network traffic to pass through, potentially exposing virtual machines to attacks. If an NSG is configured to allow traffic from any source IP address, it can allow attackers to bypass network security and gain access to virtual machines. This situation can occur if an NSG is not properly configured to only allow traffic from authorized sources, such as a specific IP address range. Tackling Misconfigured Cloud Resources To tackle the risk of misconfigured cloud resources, businesses should conduct regular security assessments to identify potential misconfigurations. Steps should include reviewing security logs, examining network traffic, and using automated tools to scan cloud resources for misconfigurations. Once misconfigurations have been identified, they should be remediated quickly to reduce the window of vulnerability. 3. Insecure Interfaces & APIs Providers offer cloud interfaces and application programming interfaces (APIs) that allow businesses to manage their cloud resources. However, these tools may be vulnerable to attacks if they are not properly secured. If attackers can exploit vulnerabilities in cloud interfaces and APIs, they may be able to gain access to sensitive data or compromise cloud infrastructure. Tackling the Risk of Insecure Interfaces & APIs The best and most effective way to secure interfaces and APIs is to follow security best practices for development and management. These steps can involve using secure coding practices, such as input validation and output encoding, to reduce the risk of injection attacks. Businesses should also ensure that APIs are properly authenticated and authorized, and use encryption to protect sensitive data in transit. Apart from securing APIs, businesses should also monitor API activity for suspicious behavior, such as excessive API calls or unusual patterns of API usage. By monitoring API activity, businesses can quickly detect and respond to potential attacks, reducing the risk of data loss or infrastructure compromise. 4. Malware Infections Malware infections are a significant cloud computing security risk as malware can be used to steal sensitive data, disrupt business operations, and infect other systems connected to the cloud environment. Malware infections can occur in several ways in a cloud environment. The most common methods include the following. Tackling Malware Infections To prevent malware infections, businesses should implement a range of security measures such as anti-malware software, network segmentation, access controls, and employee training on security best practices. Businesses should also stay up to date on the latest malware threats and work with their cloud service provider to implement security measures that are appropriate for their specific cloud environment. 5. Account Hijacking Account hijacking occurs when an attacker gains unauthorized access to a user’s account in a cloud environment. This situation can occur via several methods, including phishing attacks that trick users into revealing their login credentials, weak passwords that are easily guessed or cracked, or vulnerabilities in the cloud environment’s authentication or authorization mechanisms. Once an attacker gains access to a user’s account, they can use it to access sensitive data or systems, launch further attacks, or cause other security incidents. Tackling Account Hijacking To tackle this risk, businesses should take a multi-layered approach to security that includes a combination of
Adopting Business Intelligence (BI) To Reshape Your Organization For The Future

The famous buzzword among enterprises, both growing and well-established, is ‘Business Intelligence (BI).’ It is currently estimated that about 33% of large-scale businesses will include business intelligence in their decision-making process. As per a report published by ReportLinker, the business intelligence market is expected to thrive and grow by leaps and bounds to about $33.3 billion by 2025. It is quite apparent that business intelligence has become a crucial part of running a business and will be a major driving force behind your business transformation in the future. Along with your digital transformation efforts, you must also explore the BI space, as much of your digital transformation goals cannot be achieved without the proper use of data analytics. Here is a brief rundown of how BI can help optimize your business decisions and operations. Enhanced agility Business agility is always a good indicator of better results. Agile practices like workflow optimizations, employee skill improvement, mentorship programs, and so on foster a positive workplace and improve the company’s overall performance. And a big part of running an agile business is to adopt BI tactics. BI solutions provide the necessary data and insights business leaders need to strategize and implement effective agile methodologies in their organizations. Business analytics gives the proper metrics to assess and validate every agile effort and can thus be used as evidence to base further decision-making. Here are some ways BI can help identify solutions and improve business agility: Increased collaboration As an offshoot of agile practices, you can expect organizations to integrate their teams efficiently and operate in a positive collaborative environment. BI can help eliminate the need for various individual tools used by employees from different departments and replace it with unified, integrated systems. This will boost collaboration among the various teams. Instead of isolated data silos, teams can easily share and view data insights from a unified dashboard. For instance, the marketing team can easily collaborate with the sales team and get accurate data on current customer profiles and user behavior. Integrated systems Integrating Artificial Intelligence with business analytics will further help take advantage of the company’s digital transformation efforts and reflect positively on its performance. Furthermore, BI can also use advanced integrations with APIs and third-party systems efficiently. BI can help you quickly gather data from all your endpoints, consolidate data and get useful insights to help you make more effective decisions. It can also help you implement more efficient systems with advanced functionalities. For instance, the data from your emails and customer interaction from various channels can be used to develop AI-based chatbots. Machine learning for self-service The machine learning space is rapidly expanding, making BI software more intuitive every passing day. BI, initially touted for its predictive capabilities and insights, can very well be used to provide much deeper insights and personalized services. For instance, your BI tools can determine custom service offerings for each customer based on their preferences and specific consumer experience. BI, with the aid of machine learning, can accelerate data transformation and analytics, allowing you to quickly make sense of the huge amounts of data that get generated with each consumer interaction. And it’s not just your customers that will benefit from a self-servicing data application. With BI, data can cross boundaries beyond your traditional data teams, and everyone in the company can easily understand the insights it presents. Self-service from BI can help reduce dependencies, present uniform and consistent information across the organization and avoid data inaccuracies. As everyone can now have easy access to information, there will be fewer communication issues, better transparency, and better collaboration. Intuitive data renderings With BI, data visualizations can be made simple, more effective, and meaningful. Advanced BI tools can go beyond traditional dashboards and graphing features to give you superior innovative and engaging visualizations. You can simply type in a question, and your BI system can quickly analyze and give you the right information and insights relevant to your query. BI can not only transform your work processes but also help you innovate much faster as it becomes easier to make sense of your data. This means your stakeholder meetings and business decision-making processes will become more streamlined, evidence-based, and efficient. Real-time business intelligence Real-time business intelligence tools allow you to quickly look at current trends and any emergency event that needs quick attention. You can get alerts and notifications on your network status, any data breaches, outages, DDoS attacks, a surge in consumer complaints, and so on. Getting these alerts as soon as possible gives you a good chance at rectifying the issues before they get too big. Explore new opportunities BI can greatly help analyze the market and your target audience. You can gather data from multiple channels like your email subscription list, sales data, customer support interactions, social media handles, website stats, etc. BI can help you make sense of all this data and help you enhance your customer experience, and product roster, and even find any opportunity for further expansion. You can identify existing problems and develop the right solutions, thus capturing a whole new market. BI can also help you with predictive maintenance of your business operations and ensure you don’t leave any stone unturned when running your business at the highest performance. Let BI reshape your organization BI, undoubtedly, has a lot to offer. It all depends on the organization to harness its goodness. If you want to make the most out of BI but are unsure of the starting point, we are here to help. Contact us today to learn more.
Artificial Intelligence In Education – Are We Looking At The Next Era Of Learning And Development?
Artificial intelligence (AI) can change the scope of education by providing students with individualized and adaptable learning experiences. AI-powered systems can assess student performance data, identify areas of strength and weakness, and change education as needed. According to research, 86% of teachers believe that artificial intelligence should be a part of the education curriculum. Imagine a world where students have access to 24/7 AI-powered virtual assistants and tutors. These advanced technologies can customize the learning experience to each student’s pace, helping bridge the education divide and ensuring equal access to high-quality education for all. But are we truly on the cusp of a revolutionary new era in education with AI? Let’s explore this exciting possibility and uncover the mystery together. 5 Ways AI is Impacting the Education Sector The widespread incorporation of technology into educational settings is causing profound shifts in the ways we instruct and are being instructed. One of the innovative approaches that can personalize the educational experience for a variety of learning groups, instructors, and students is the use of Artificial Intelligence (AI). The following are some of the ways AI directly impacts the education sector: Ensuring Access to Students with Special Needs Students who struggle academically can now find more effective communication methods thanks to cutting-edge Artificial Intelligence (AI) tools. Special students, such as those who are deaf, blind, or have autism spectrum disorder (ASD), can now participate in the educational system because of AI. AI can be used to enhance the learning experiences of special children who have a unique set of requirements to deal with. Better Tutoring for Students Personalized study plans are constantly updated to account for students’ areas of weakness that can be addressed via individualized instruction. Students with access to private tutors and extra assistance outside class are more likely to succeed. In the classroom, instructors can save a lot of time with the help of AI tutors since they won’t have to spend as much time on difficult subjects. Chatbots driven by Artificial Intelligence (AI) or virtual personal assistants powered by AI save children time. They no longer have to go to their teacher or parent for extra help. They can use put that time for other educational purposes. Simplifying Task Automation Teachers can use AI to streamline administrative chores like grading, evaluating, and responding to students’ inquiries to save time. By having AI handle several mundane duties, educators can focus on student feedback, professional development, and improving the overall classroom experience. Help Produce Smart Content Smart Content refers to content that can be automatically personalized, optimized, and adapted based on the user’s needs, preferences, behavior, and context. It leverages data and machine learning algorithms to provide a personalized experience to the user and improve their engagement with the content. The following are some of the ways AI can help produce Smart Content for education: Learning Content Updates – AI also helps create and maintain the classes’ content, ensuring that students always have access to the most recent knowledge while catering to their individual learning styles. Information Visualization – Artificial Intelligence can enable novel methods of experiencing data, including visualization, simulation, and online learning settings. Digital Lessons – With the help of AI, you can explore a wide variety of learning resources, including interactive digital interfaces with personalization choices, digital textbooks, study aids, and snippets of courses. Personalizing Education Using conversational AIs, educators can assess a student’s current level of knowledge and use that information to create a custom study plan that fills in gaps. By adjusting course content based on everyone’s strengths and weaknesses, AI helps students make better use of their time in the classroom. How is AI Set to Change the Education Market for Good in the Upcoming Years? AI is set to change the education market in the following ways: Predictive Analytics AI can be used to assess student data to predict future academic performance. This allows teachers to detect possible academic problems early on and take corrective action. Online Education AI can help students with online education by improving the accessibility of content from any part of the world. With the help of AI in education, students now have access to real-time chatbots and tutoring platforms. This helps students with better learning. For example, students can learn some useful things in which they lacked expertise before. Moreover, AI has helped develop tools that can test students’ skills to improve their learning ability. Gamification of Learning AI can help gamify learning by making education more engaging, interactive, and personalized. By incorporating AI into education, students can have a more enjoyable and effective learning experience. AI can help to create gamified rewards systems that incentivize students to learn by offering rewards such as badges, points, and virtual prizes. Automated Assessment and Feedback AI can analyze students’ performance, providing accurate evaluation and feedback in real-time, which helps educators discover areas of strength and weakness and change education appropriately. Virtual Educators and Assistants Students can study at their own pace and get support whenever they need it from virtual assistants and tutors driven by Artificial Intelligence (AI). A Few Potential Benefits of Using Artificial Intelligence in The Education Sector The following are some of the prevalent benefits of AI learning for students: The Bottom Line: Artificial Intelligence is Set to Change the Education Industry for Good! Artificial intelligence (AI) has the potential to transform education and the way we learn and grow. It has the potential to offer equitable access to high-quality education for everyone by personalizing learning, providing 24/7 help, and bridging the education gap. While additional research and development are required to fully achieve the promise of AI in education, it is obvious that we are entering the next phase of educational learning and development with AI. It is critical that we continue to investigate and invest in this innovative technology to reap its numerous advantages for students and educators alike.
A Developer’s Guide to Solidity: Why Choose Solidity for Blockchain Development Projects?

First proposed by Gavin Wood, CTO of Ethereum, in 2014, Solidity is an object-oriented, high-level programming language for writing smart contracts on the Ethereum blockchain. Although other languages like Vyper, Bamboo, LLL, Serpent, etc., were used for writing smart contracts on the Ethereum blockchain, Solidity was quick to gain traction in the market. So, what led to the growing popularity of Solidity? Its swift acceptance can be attributed to a few key factors. Before we dive deeper into Solidity and its significance, let’s first have a look at smart contracts. What Is a Smart Contract and How Does It Work? A smart contract in a blockchain is a self-executing contract with the terms of the agreement written directly into code and stored on a blockchain network. Smart contracts are created using programming languages like Solidity and are stored on a blockchain. They can be used to facilitate, verify, and enforce the negotiation or performance of a contract. They allow for the automation of contract execution and enforcement, which means that once certain conditions are met, the contract will execute itself automatically. For example, imagine a smart contract that governs the purchase of a car on a blockchain network. The contract would be programmed with the terms of the sale, such as the price, the vehicle’s make and model, and the buyer’s and seller’s identities. The buyer would then transfer the agreed-upon amount of cryptocurrency to the smart contract, and the contract would automatically transfer ownership of the car to the buyer and release the funds to the seller. This entire process would be transparent, traceable, and secure, as it is recorded on the blockchain. In summary, smart contracts in blockchain are digital contracts that contain the rules, penalties, and the parties involved in an agreement, with the code and the agreements contained therein existing over a decentralized blockchain network. Now that you have a brief overview of smart contracts, let’s have a look at the basics of smart contracts on the Ethereum network. Ethereum Network & Smart Contracts Ethereum is a decentralized, open-source blockchain platform that enables the creation of smart contracts and decentralized applications (dApps). Smart contracts on the Ethereum network are written in the programming language Solidity and are stored on the Ethereum blockchain. Here is an overview of how smart contracts work on the Ethereum network: In summary, smart contracts on the Ethereum network are self-executing contracts that are stored on the Ethereum blockchain and written in the programming language Solidity. They can be used to facilitate, verify, and enforce the negotiation or performance of a smart contract. Understanding Solidity – The Key Features of Solidity Solidity is a high-level programming language designed for developing smart contracts on the Ethereum blockchain. It was developed by the Ethereum Foundation to enable developers to create dApps that can run on the Ethereum network. 1. Object-Oriented Programming Model One of the key features of Solidity is its contract-oriented programming model, which allows developers to create self-executing contracts that have the terms of the agreement written directly into the code. This capability allows for the transparent, tamper-proof, and autonomous execution of agreements. 2. Familiar Syntax The syntax of solidity, inspired by JavaScript, is designed to be easy to learn for developers with a background in object-oriented programming languages like C, C++, and Java, making it a popular choice among developers. For a developer with experience in object-oriented programming languages, it won’t be difficult to learn Solidity. It is important to understand, however, that though Solidity looks similar to JavaScript, it’s a completely different beast under the hood. 3. Larger Developer Community Solidity has a larger developer community with experienced Solidity developers who can help answer questions and provide guidance. This resource can be especially useful for developers who are new to blockchain development or who are working on a particularly complex project. A large developer community also means a lot of open-source libraries and frameworks are available to developers, which can make development faster and more efficient. As a result, developers can focus on the unique aspects of their projects and not have to worry about building everything from scratch. 4. Availability of Tools & Frameworks Due to its popularity and widespread use, Solidity developers can choose from many tools and frameworks such as Truffle, Embark, DappHub, OpenZeppelin, Mythril, etc. These tools and frameworks can help developers to streamline the development process, improve the security and reliability of their smart contracts, and interact with the Ethereum blockchain more easily. What Are the Skills Required for a Solidity Developer? Solidity is a programming language that is used to write smart contracts for the Ethereum blockchain. To be a successful Solidity developer, one should have the following skills Strong problem-solving skills: A Solidity developer should have strong problem-solving skills to identify and resolve any issues that arise during the development process. Solidity – The Go-to Language for Blockchain Development Projects Solidity is a powerful and flexible programming language that is well-suited for developing smart contracts on the Ethereum blockchain. With its user-friendly syntax and extensive support for complex data structures, Solidity makes it easy for developers to create, test, and deploy smart contracts that can automate complex business processes and bring transparency and trust to a variety of applications. In addition to its robust feature set, Solidity also benefits from a large and growing developer community, who contribute to the language’s ongoing evolution and share best practices and tools for working with it. Whether you are a seasoned developer or just getting started with blockchain development, Solidity provides a solid foundation for building innovative and secure blockchain applications.
7 Proven Data Loss Prevention Techniques to Keep Your Business Safe and Secure

According to a report by Cybersecurity Ventures, cybercrime will cost the world $10.5 trillion annually by 2025. With the increasing threat of cyber attacks, data breaches, and human error, it’s more important than ever to take steps to protect your company’s sensitive information. In this blog post, we’ll discuss seven proven techniques that can help keep your business safe and secure. From employee training to security software, data encryption, and disaster recovery planning, these techniques will give you a solid foundation for preventing data loss and safeguarding your company’s valuable assets. What is Data Loss Prevention? Data Loss Prevention (DLP) is a security strategy to detect, monitor, and prevent the unauthorized or accidental sharing of sensitive information. DLP solutions are used to identify and protect sensitive data, such as credit card numbers, Social Security numbers, and confidential business information from being lost, stolen, or misused. The goal of DLP is to protect an organization’s sensitive information and keep it confidential. It can be achieved by monitoring, detecting, and preventing sensitive data from being transferred, stored, printed, and shared in an unauthorized manner. DLP solutions can be implemented in a variety of ways — including through software, hardware, or a combination of both — and can be applied to various types of data and communications, such as email, file transfers, and instant messaging. How Does Data Loss Prevention Work? DLP typically works by identifying, monitoring, and protecting sensitive data using various technologies and methods such as: 1. Data discovery: DLP solutions scan and identify sensitive data based on predefined criteria, such as credit card numbers or Social Security numbers. This process helps organizations understand what sensitive information they have and where it is located. 2. Data monitoring: DLP solutions monitor network traffic, email, and other forms of communication for sensitive data. This capability helps organizations detect and prevent data breaches, data exfiltration, and other malicious activities. 3. Data protection: DLP solutions can take various actions to protect sensitive data, such as encrypting, blocking, or quarantining sensitive information. 4. Data governance: DLP solutions can be used to enforce policies and procedures related to the handling of sensitive data, such as data retention, data archiving, and data deletion. 5. Data loss prevention policies: DLP solutions can be configured to enforce data security policies and compliance regulations by preventing sensitive data from being sent to unauthorized recipients, blocking the use of unsecured communication channels, and alerting security personnel to potential data breaches. 6. Reporting and analysis: DLP solutions can provide detailed reporting and analysis of data loss incidents, which can be used to improve security policies and procedures. In short, DLP solutions work by identifying, monitoring, and protecting sensitive data, and allowing organizations to take appropriate actions to prevent data breaches and protect sensitive information. What Are The Types of Data Loss Prevention Solutions? Several types of DLP solutions are available, each of which addresses different aspects of data security: 1. Network DLP: These solutions monitor network traffic and identify sensitive data as it moves across the network. They can also block or quarantine sensitive data to prevent it from being transferred to unauthorized locations. 2. Endpoint DLP: These solutions run on individual devices, such as laptops and smartphones, and monitor for sensitive data on those devices. They can also prevent sensitive data from being copied to removable storage devices or shared via email or instant messaging. 3. Cloud DLP: These solutions monitor and protect sensitive data in cloud-based storage and collaboration platforms, such as Google Drive and Dropbox. 4. Email DLP: These solutions monitor and protect sensitive data in email messages, attachments, and other forms of electronic communication. They can also prevent sensitive data from being sent to unauthorized recipients. 5. Application DLP: These solutions monitor and protect sensitive data within specific applications, such as CRM, ERP, and accounting software. 6. Data Discovery DLP: These solutions scan data storage to identify and classify sensitive data based on predefined criteria, such as credit card numbers or Social Security numbers, and allow organizations to monitor and protect it. 7. Mobile Device DLP: These solutions monitor and protect sensitive data on mobile devices, such as smartphones and tablets, and can prevent sensitive data from being copied to removable storage devices or shared via email or instant messaging. Overall, the type of DLP solution that an organization chooses will depend on the specific data security needs and requirements of the organization. Seven Data Loss Prevention Best Practices to Keep Your Business Safe & Secure 1. Regularly Assess Your Data: Regularly assessing and identifying sensitive data is an essential step in data loss prevention. This process involves identifying and locating all sensitive data within your organization, including personal information, financial data, and confidential business information. There are a few ways to achieve this. I. Data Discovery: Use specialized software to scan your organization’s data storage systems, including servers, workstations, and mobile devices, to identify sensitive data based on predefined criteria, such as credit card numbers or Social Security numbers. II. Data Inventory: Create a comprehensive inventory of all sensitive data within your organization, including where it is stored, who has access to it, and how it is being used. III. Data Classification: Classify data based on its sensitivity and value to the organization to identify and protect the most critical data. IV. Risk Assessment: Conduct a risk assessment to identify potential threats to your sensitive data and the likelihood of a data loss event occurring. Once you have identified and located your sensitive data, you can take steps to protect it, such as implementing data encryption, access controls, and security software. Regularly assessing and identifying your sensitive data also allows you to keep your data security practices up to date and identify any new threats as they arise. 2. Implement a Data Classification System Implementing a data classification system is an essential part of data loss prevention. This process involves assigning labels or tags to different types of data based on their sensitivity and value to the organization. By
The Emergence Of Electric Vehicle Software

About a couple of decades ago, futuristic renditions of automobiles looked like flying cars and space travel. While we may not yet be traveling in flying taxis, the future of automobiles is already defined and is traveling in the direction of electric vehicles (EV). With Tesla introducing groundbreaking luxury EVs to the market, the world has woken up to the big potential that EVs hold. EVs are also the current solution to the concern about dwindling fuel resources and the pollution problems from fossil resources. The global EV market is only growing every year. It is expected to reach USD 1103.17 billion by 2030, and several governments worldwide are gearing up to transform their automobile scene to be predominantly EV based. Currently, EVs make up just 3% of the new vehicles in the US, but by 2030, the goal has been set to make this percentage go as high as 50%. While government policies may be crafted based on environmental factors, the acceptability of these vehicles still rests with the customers. Many people associate value with their cars and have several differentiating factors in choosing traditional internal combustion engine-based cars. These cars run on fossil fuels and vary in how they work, the fuel used, and the corresponding effect on the driver and travel experience. But when it comes to EVs, the exact machinations and technology behind the car are more than just mechanical. The parts are smaller, more compact, and have more of a standardized way of working from the mechanical perspective. What would set apart an EV would be the software used. EV makers will have to focus just as hard on their software as they do on their hardware because it is with software that they can provide value-added services and a distinguishable advantage over their competitors. EV software is thus gaining a lot of traction both with automobile manufacturers and service providers who have rightly capitalized on the growing popularity of the EV market. As the market matures, you could also witness a highly advanced and evolving EV software market. Electric Vehicle Software Electric vehicle software can be a huge space where you can find a generic comprehensive software package delivering a multitude of services and feature-specific software packages focusing on just particular functionalities. For instance, the autonomous driving feature of Tesla, Tesla Autopilot, provides full self-driving capabilities. On the other hand, you could also download navigational software to be used in your EVs. Some common software products come into the picture when you think about operating EVs: 1. EV Fleet management If you want a successful EV adoption among the masses, it must come with the proper infrastructure support for charging stations and alternate charging facilities. This especially rings true for companies buying or leasing multiple EVs as they would need a proper management system to take care of their EV fleet operations and ensure regulations compliance. EV fleet management software is used to manage EV fleets with features like: 2. Virtual prototypes for EVs Another type of EV-based software gaining prominence is the software used to prototype EVs. This type of software helps emulate the complex electromechanical components and the interaction between the software and hardware pieces in the form of virtual prototypes. Virtualization software helps develop EVs and test them in virtual environments without undergoing expensive physical prototyping and testing. 3. Digital cockpit With EVs becoming a computing system on their own, it is fair to make them more in alignment with a digital driving experience. Digital cockpit software provides an all-digital dashboard system that can replace old steering wheels and gearboxes. 4. Intelligent mobility solutions When you add digitalization to any machine, it becomes a connected device essentially. The computers that we use today are almost always connected as it is essentially useless otherwise. Similarly, EVs can also use SaaS-based smart mobility solutions to become smarter. These solutions, along with the Internet of Things, can be further exploited to create an optimized and personalized user experience. For instance, your EV can immediately get alerts on traffic status, send alerts in case of an emergency, schedule maintenance, and so on automatically by collecting real-time data from the vehicle sensors. 5. Software for self-driving cars A lot of money and effort is being spent on autonomous or self-driving cars. Big names like Google and Tesla are already putting their AI self-driving cars to the test, and we could soon expect these cars to run on our roads, given the legal and compliance roadblocks are solved. Electric vehicles software will propel the growth of EVs As mentioned earlier, EVs will probably act as connected devices beyond your traditional cars. So the question arises: Do you gain complete ownership of your EV? As an EV comes preloaded with software, just like your smartphone, you may not be able to claim complete ownership of the software in your EV. And with software, you also need to ensure compliance and stay up to date with the latest upgrades. Besides these questions, there are also considerations regarding driver performance concerns. With a self-driving car or a digital cockpit system, it can be expected that driver errors will be reduced to a greater degree. What would it mean in terms of claiming insurance or finding faults in case of an accident? As the EV market continues to evolve and more EV software comes into use, all the considerations must be addressed.
7 Ways DevOps Accelerates Digital Transformation

DevOps combines software development (Dev) and IT operations (Ops) to accelerate the delivery of software products and services. This methodology prioritizes collaboration, automation, and measurement to improve the speed and quality of software delivery. The three key principles of DevOps include: DevOps addresses many of the challenges that arise when trying to deliver software products and services in a rapidly changing digital landscape. By implementing DevOps best practices, organizations can gain a competitive edge and drive digital transformation in their industries. How DevOps Makes Digital Transformation Easier and Faster DevOps makes digital transformation easier and faster by implementing several key practices and principles that align development and operations teams and improve collaboration, speed, and quality. All of these practices and principles ultimately allow organizations to deliver software and services faster with higher quality and reliability. As a result, they can quickly respond to changing market conditions and customer demands, as well as improve overall performance and competitiveness, which is crucial for digital transformation success. Seven Ways DevOps Accelerates Digital Transformation DevOps has become an essential tool for organizations looking to drive digital transformation because it addresses many of the challenges that arise when delivering software products and services in a rapidly changing digital landscape. DevOps accelerates digital transformation in seven ways. 1. Faster Time to Market DevOps allows for faster time to market by streamlining the development, testing, and deployment process. This is particularly important in today’s digital economy where organizations must quickly respond to changing customer needs and market conditions. CI/CD practices allow organizations to test and deploy new software and features quickly, without risking service disruptions. As a result, organizations can bring new products and services to market faster, which is particularly important in today’s digital economy where customers have more options and shorter attention spans. 2. Collaboration DevOps promotes collaboration between development and operations teams by breaking down silos and fostering a culture of cooperation and shared responsibility. Practices such as CI/CD allow development and operations teams to work together to deliver software products and services more efficiently. With improved collaboration and communication, development and operations teams can work together to identify and address issues more quickly and effectively, which leads to increased agility and flexibility. It allows organizations to pivot and adapt to new technologies and business models quickly, as they can identify and implement changes more efficiently. 3. Reduced Risk & Increased Stability DevOps practices are designed to reduce risk and increase stability by automating and streamlining the software development process. CI allows development teams to integrate code changes into a shared repository multiple times a day, enabling frequent testing and early detection of issues. This strategy reduces the risk of errors and improves the overall stability of the software. CD allows development teams to release new software and features to customers quickly and efficiently. By automating the deployment process, organizations can deploy new software and features in a controlled and predictable manner, reducing the risk of service disruptions. Together, CI/CD practices allow organizations to test and deploy new software and features quickly, without risking service disruptions. In addition, DevOps practices also employ monitoring, testing, and continuous feedback to enable early detection of issues and allow organizations to respond quickly, thus reducing risk and increasing stability. 4. Better Scalability of Products By aligning development and operations with business objectives, DevOps helps to ensure that the software development process focuses on delivering value to customers. This practice leads to better scalability and reliability of software products and services, as development teams are able to prioritize and implement features that will have the greatest impact on the business and its customers. DevOps also promotes the use of automation and monitoring, which helps to ensure that software products and services are reliable and scalable. By automating routine tasks, development teams can focus on delivering new features and functionality, while operations teams can focus on maintaining the stability and performance of the software. 5. Higher Quality & Bug-Free Products DevOps practices such as testing and monitoring play a crucial role in ensuring higher quality products and reducing the number of bugs and issues. Testing is a fundamental part of the DevOps process, and it is integrated into the development process through practices such as CI/CD. As a result, code changes are tested automatically and continuously, which allows for early detection of issues and reduces the risk of errors. Additionally, DevOps encourages the use of automated testing, which increases the speed and efficiency of testing and helps to ensure that software products and services are of high quality. Monitoring is another important aspect of the DevOps process, which helps to ensure the reliability and stability of software products and services. Continuous monitoring and monitoring as code practices help organizations track and measure the performance of their software products and services, which allows them to identify and address issues more quickly. By continuously testing and monitoring, DevOps helps organizations to detect issues early and fix them before they become major problems, thus ensuring higher quality products and reducing the number of bugs and issues. In addition, DevOps promotes the use of continuous feedback, which allows development and operations teams to collect and act on feedback from customers and end-users. That process helps to improve the quality of products and services. 6. Stabilized Workflow DevOps stabilizes workflows by promoting the use of automation, testing, and monitoring throughout the software development process to ensure that software products and services are reliable and stable. Additionally, DevOps also promotes the use of metrics and data-driven decision-making, which allows development and operations teams to understand the performance of their software products and services, as well as make informed decisions that improve the stability and reliability of the software. 7. Automated Infrastructure Management DevOps can automate infrastructure management by using tools and techniques that allow for the automated provisioning, configuration, and management of IT infrastructure. One of the key tools used to automate infrastructure management in DevOps is infrastructure as code (IAC). IAC allows organizations to
How Can Companies Protect Their Data in Cloud Environments? Here are the Challenges and Best Practices

In today’s digital age, it is increasingly common for companies to store their data in cloud environments. While this can provide numerous benefits, it also poses potential security risks. Hackers and cybercriminals may try to access sensitive data stored in the cloud, and data breaches can seriously harm businesses. Therefore, companies need to take steps to protect their data in the cloud. However, if you own a company and don’t know what challenges you’ll face in protecting your data in a cloud environment, you’re in the right place. In this article, we’ll explore four challenges companies face in securing their data in the cloud, as well as four practices to follow to ensure data safety and privacy. Why Is It Important for Companies to Protect Their Data in Cloud Environments? Moving and managing infrastructure and assets to the cloud has been more popular over the last decade as businesses have discovered the benefits. The wide spread of COVID-19 has only made this move faster. In recent years, there has been a shift toward hiring freelancers and contract workers rather than traditional full-time employees. Therefore, it is critical to safeguard the access to and transfer of company data across multiple unknown networks and the cloud. Businesses may benefit from cloud data protection in several ways, including improved data visibility, integrity, and security, simplified data storage management, more informed decision-making, and the creation of a more robust disaster recovery strategy. Additionally, data security in the cloud can assist in cutting administrative and IT expenses. Finally, compliance with laws and regulations, such as the General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA), may require companies to take certain steps to protect the data they store in the cloud. By following best practices for data protection in the cloud, companies can ensure that they follow these laws and regulations. What Are the Challenges A Company Will Face in a Cloud Environment? The use of cloud computing has become increasingly popular in recent years as a means of storing and accessing data and applications. While the cloud offers many benefits, including reduced IT costs and increased flexibility, it also introduces data protection challenges. A company can be subject to the following challenges to protect its data in cloud environments: 1. Security risks One of the main challenges in protecting data in the cloud is the risk of cyber-attacks and data breaches. These threats can compromise the security of data stored in the cloud, potentially leading to the loss or theft of sensitive information. To address this risk, companies must implement robust security measures such as encryption and authentication to protect against unauthorized access to their data. 2. Regulatory compliance Another challenge in protecting data in the cloud is the need to comply with various regulations governing the handling and protection of data. Ensuring compliance with these regulations can be a complex and time-consuming process, particularly in a cloud environment where data may be stored and accessed by multiple parties. 3. Data Privacy In addition to regulatory compliance, companies must also consider the privacy rights of individuals whose data they collect and store. Privacy can be especially challenging in the cloud, where data may be accessed by multiple parties and stored in different locations worldwide. Companies must implement appropriate measures such as consent forms and secure data handling policies to protect data privacy. 4. Data loss or corruption Another challenge in protecting data in the cloud is the risk of data loss or corruption due to factors such as hardware failures or software glitches. To mitigate these risks, companies must have contingency plans to ensure their data’s availability in the event of an incident. This may include implementing backup and recovery systems or using multiple cloud providers to reduce the risk of a single point of failure. Best Practices to Protect Data in Cloud Environments Data protection is a crucial concern for businesses of all sizes, particularly for cloud computing. Cloud services have become increasingly popular in recent years as a means of storing and accessing data and applications. Still, it introduces a set of challenges related to data protection. In this section, you’ll discover some best practices companies can follow to protect their data in cloud environments. 1. Implement robust security measures Implementing robust security measures is one of the key best practices for protecting data in the cloud. This process includes using encryption to protect data in transit and at rest and implementing authentication measures such as two-factor authentication to prevent unauthorized access to data. In addition, companies should also consider using security tools such as firewalls and intrusion detection systems to protect against cyber-attacks and other threats. 2. Choose a reputable cloud provider You need to choose a reputable and reliable cloud provider. The right vendor can help to minimize the risk of data loss or corruption due to hardware failures or other issues. In addition, companies should carefully review the terms of service and security measures of potential cloud providers to ensure that their data will be protected per their requirements. 3. Develop a robust data governance strategy Another tool is developing a robust data governance strategy. This practice should include policies and procedures for handling and storing data and measures to ensure compliance with relevant regulations such as GDPR and the Health Insurance Portability and Accountability Act (HIPAA). Companies should also consider implementing a data classification system to identify and protect sensitive or confidential data. 4. Implement a robust backup and recovery strategy Another important best practice for protecting cloud data is implementing a robust backup and recovery strategy. This should include regular backups to ensure data can be recovered during a disaster or other incident. Companies should also consider using multiple cloud providers to reduce the risk of a single point of failure and ensure the availability of their data. Conclusion Protecting data in a cloud environment involves addressing various challenges related to security, compliance, and data loss or corruption. By implementing the practices discussed
