HIPAA-compliant software protects patient data through encryption, robust access controls, continuous monitoring, and compliant infrastructure. Security must be integrated into design, development, and operations to safeguard sensitive health information across all systems and over time.
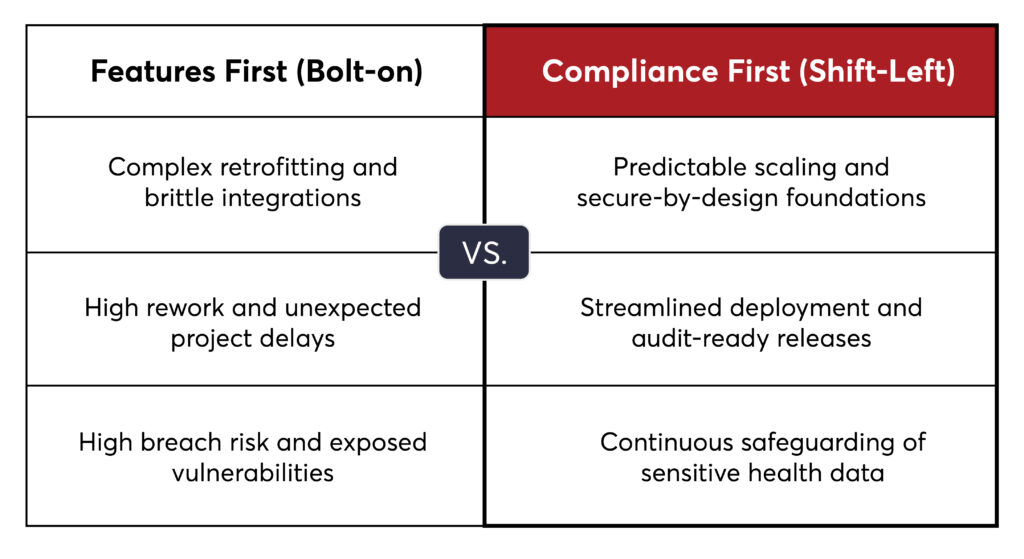
In practice, compliance often fails because it is addressed too late, not due to a lack of tools. Teams that prioritize features over early compliance face rework, delays, and security vulnerabilities.
This blog outlines key steps for building compliant healthcare systems and emphasizes the importance of early compliance planning.
Building HIPAA-compliant healthcare software requires a structured approach that covers both technology and process. It’s not a single control or tool, but a coordinated set of measures to protect patient data throughout its lifecycle.
Begin by focusing on the data, since everything relies on it. PHI must remain secure at all times, whether it is stored, processed, or shared between systems. If data protection is weak, compliance cannot be maintained.
Not all users need access to all information. Strong access controls reduce internal risks, which are among the most common causes of breaches in healthcare systems.
It’s important to know how data is accessed and used. If you don’t track this, you can’t hold anyone accountable or respond well to incidents.
Healthcare systems are interconnected, and each integration can bring new risks. Protecting these connections is essential for keeping healthcare data safe.
Most security failures occur because the infrastructure is set up incorrectly, not because there aren’t enough tools. Building a solid foundation helps prevent many future risks.
Compliance is an ongoing process. It needs to adapt as new threats appear, systems change, and regulations are updated.
Many teams put off compliance, assuming they can handle it later. This often leads to unnecessary complexity and risk as their systems grow. Other reasons include:
As a result, teams face extra work, project delays, and gaps in healthcare software compliance.
Building secure healthcare applications takes both technical skill and a real understanding of the healthcare field. It’s more than just adding security features. You need systems that remain secure, comply with regulations, and adapt as needs change.
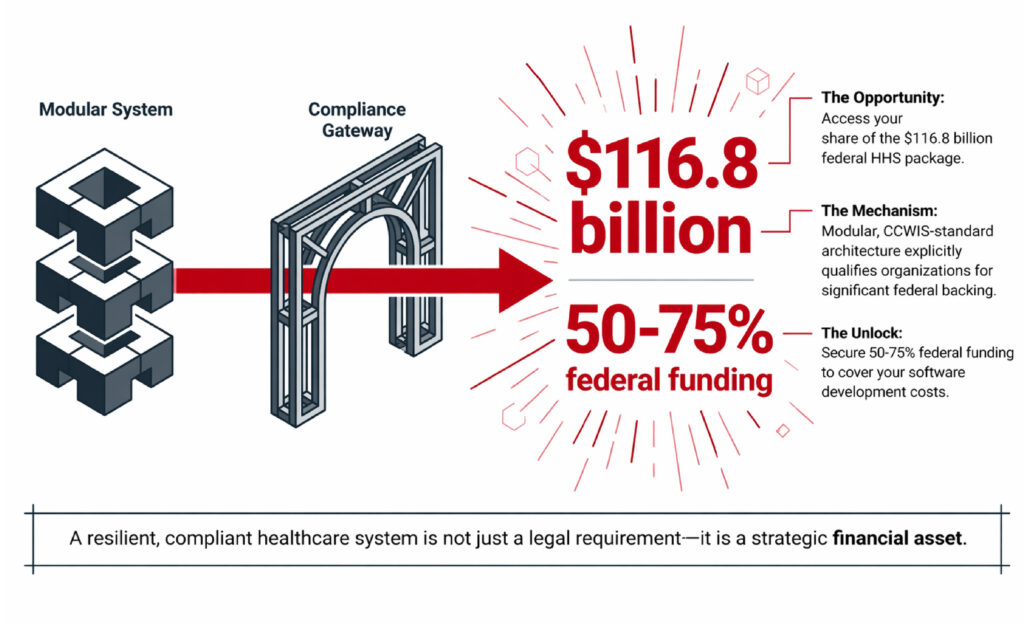
At InApp, we go beyond just building software. With our modernization-in-place approach, you can upgrade your system gradually while keeping your key services running. Instead of a single system, we offer separate but connected modules for tasks such as intake, case management, and financial tracking. Each module is built to meet federal CCWIS standards.
This modular approach provides your system with greater flexibility and reliability. It can also help you qualify for federal funding that covers 50-75% of development costs.
What are you waiting for? Access your share of the $116.8 billion federal HHS package by building a resilient, compliant healthcare system.
HIPAA-compliant software keeps patient data safe by using encryption, access controls, audit logs, and secure infrastructure. It also relies on clear processes and policies.
No. Staying compliant means you need to monitor, update, and regularly check for risks.
Yes. If third-party systems are not secured and monitored, they can create security risks.
Yes, but only if you make compliance part of the design and development process right from the start.
Data protection is key. If PHI is not secure, no other controls can make up for that risk.